By Jim Shimabukuro (assisted by ChatGPT)
Editor
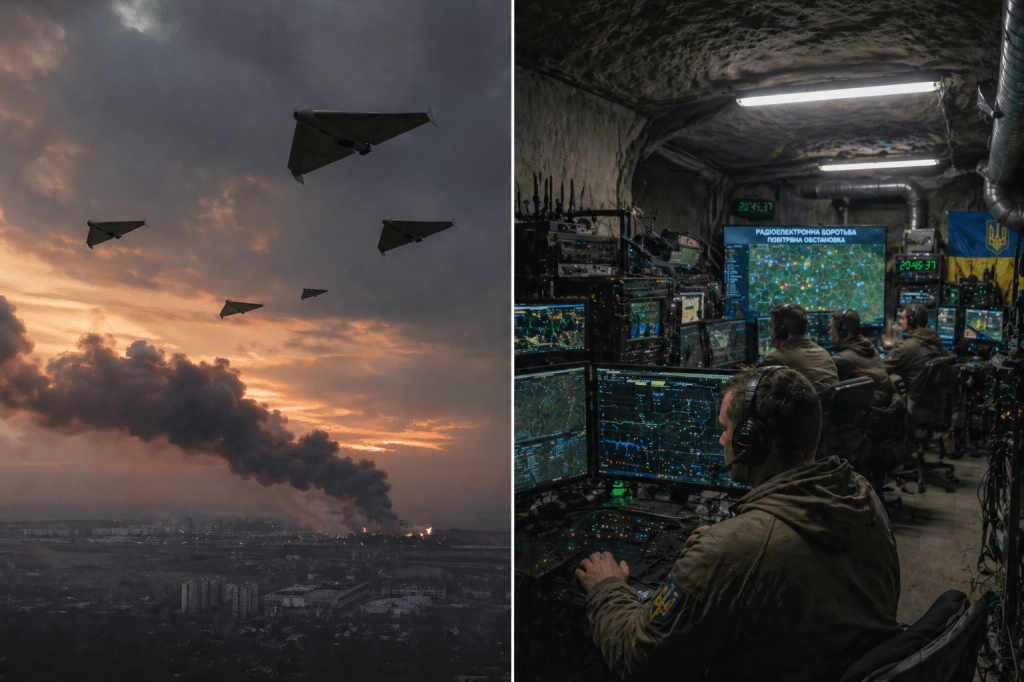
Both Ukraine and Russia are actively trying to disrupt, hijack, or otherwise neutralize enemy unmanned systems, and in limited cases they can effectively “turn” those systems into wasted or even counterproductive assets. However, fully commandeering an enemy drone or ground robot and repurposing it as your own weapon is still rare, technically difficult, and situational. What is widespread—and increasingly decisive—is a spectrum of electronic warfare (EW), spoofing, interception, and cyber operations that can achieve many of the same battlefield effects without literal takeover.
At the most mature level, both sides are using electronic warfare to break or manipulate the control links between operators and drones. Modern battlefield drones typically rely on radio-frequency (RF) links, GPS/GNSS navigation, or—in newer systems—fiber-optic tethers. EW systems can jam these signals, severing the operator’s control, or spoof them by injecting false positioning data. Ukraine’s “Pokrova” system, for example, can replace satellite navigation signals and mislead Russian drones into flying off course or crashing [1]. This is not “hijacking” in the cinematic sense, but it can effectively neutralize or redirect a drone—sometimes causing it to land intact, where it may be recovered and reused.
More advanced forms of interference blur the line between denial and takeover. If an attacker can impersonate the control signal (for example, by overpowering the legitimate operator’s transmission), they may gain partial control of the drone. In practice, this is difficult because many systems use encryption, frequency hopping, or proprietary protocols. Still, the sheer volume of commercial off-the-shelf drones (DJI-class quadcopters, improvised FPVs) used by both sides introduces vulnerabilities: these systems are often less secure, making them more susceptible to takeover or forced landing. Reports from the war consistently note that EW units on both sides can capture or redirect poorly secured drones, though this is opportunistic rather than systematic.
Cyber operations extend this contest beyond the battlefield. Ukrainian-linked hackers have penetrated Russian drone companies and infrastructure, destroying data and disrupting production pipelines [2]. While this does not directly hijack drones in flight, it targets the broader ecosystem—firmware, supply chains, and command networks—that could, in theory, enable deeper exploitation. Similarly, signals intelligence units—such as Russia’s “Rubicon” drone warfare center—focus on locating drone operators and control nodes, effectively attacking the human “link” in the control loop rather than the drone itself [3]. In this sense, “usurping control” often means killing or displacing the operator rather than reprogramming the machine.
A related and rapidly evolving tactic is interception by other drones. Ukraine’s “Sting” interceptor drones, for instance, physically destroy incoming UAVs, accounting for a large share of downed Russian systems [4]. While this again does not convert enemy drones into friendly assets, it reflects a broader trend: it is usually cheaper and more reliable to disable or destroy an enemy drone than to capture and reuse it. That said, when drones are forced to land intact through jamming or spoofing, they can be reverse-engineered, repurposed, or redeployed—creating a secondary pathway for “conversion.”
The emergence of fiber-optic-controlled drones highlights the limits of takeover strategies. These drones are immune to radio jamming because they are physically tethered to the operator by a cable, making them extremely resistant to EW interference [5]. Their growing use suggests that both sides recognize the vulnerability of wireless control links and are adapting accordingly—reducing the feasibility of signal-based hijacking.
In practical terms, then, “drone hijacking” in the Russia–Ukraine war is best understood as a continuum of effects: from jamming (denial), to spoofing (misdirection), to rare cases of signal takeover (control), to post-capture reuse (conversion). The strategy is absolutely realistic and already central to the war, but it rarely looks like one side cleanly seizing control of an enemy swarm and turning it back on its owner. Instead, the dominant paradigm is disruption first, exploitation second.
Looking forward, the trajectory suggests incremental movement toward more sophisticated forms of control. As autonomy increases—through onboard AI and preprogrammed targeting—the value of hijacking may actually decline, because there is less external control to seize. Conversely, if vulnerabilities are found in software stacks or AI models, future conflicts could see algorithmic or cyber-level takeovers rather than RF-level hijacking. For now, however, the battlefield reality is more pragmatic: it is far easier to confuse, crash, or intercept a drone than to steal it mid-mission and turn it into your own weapon.
References
[1] “Ukraine and electronic warfare” – https://en.wikipedia.org/wiki/Ukraine_and_electronic_warfare
[2] “Ukrainian hackers say they compromised a major Russian drone company” – https://www.tomshardware.com/tech-industry/cyber-security/ukrainian-hackers-say-they-compromised-a-major-russian-drone-company-destroying-data-backups-and-systems
[3] “Center for Advanced Unmanned Technologies ‘Rubicon’” – https://en.wikipedia.org/wiki/Center_for_Advanced_Unmanned_Technologies_%22Rubicon%22
[4] “Sting (drone)” – https://en.wikipedia.org/wiki/Sting_(drone)
[5] “Aerial warfare in the Russo-Ukrainian war” – https://en.wikipedia.org/wiki/Aerial_warfare_in_the_Russo-Ukrainian_war
Filed under: Uncategorized |












































































































































































































































































































































































































































Leave a comment